LTE Authentication. Delving into the underlying crypto… | by Sudheesh Singanamalla | uwcse-ictd | Medium

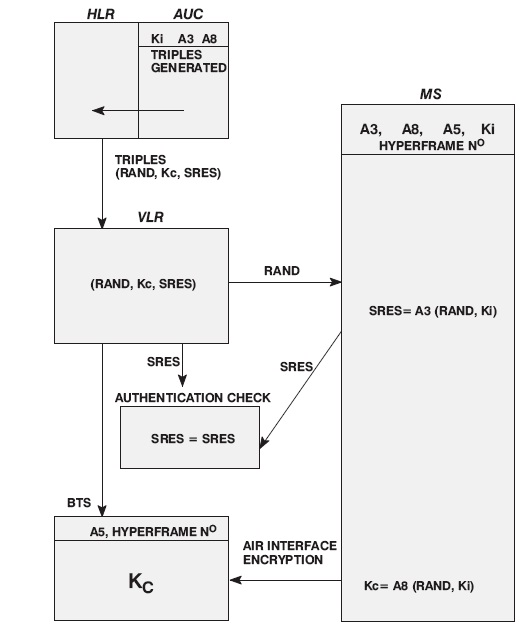
K-Tec - When you place SIM card on mobile and switch on your mobile , registration process starts to be implemented so mobile can communicate with mobile network. But in this case

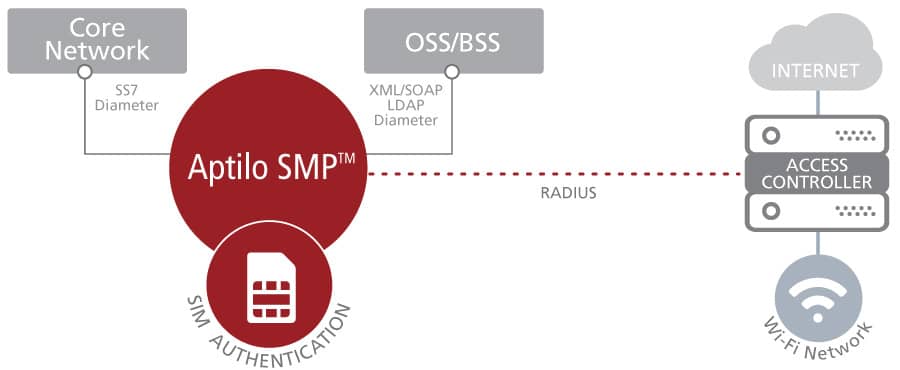
Authentication in the Cellular Phone World: EAP-SIM :: Chapter 9. Upper-Layer Authentication :: Part II: The Design of Wi-Fi Security :: 802.11 security. wi-fi protected access and 802.11i :: Networking :: eTutorials.org