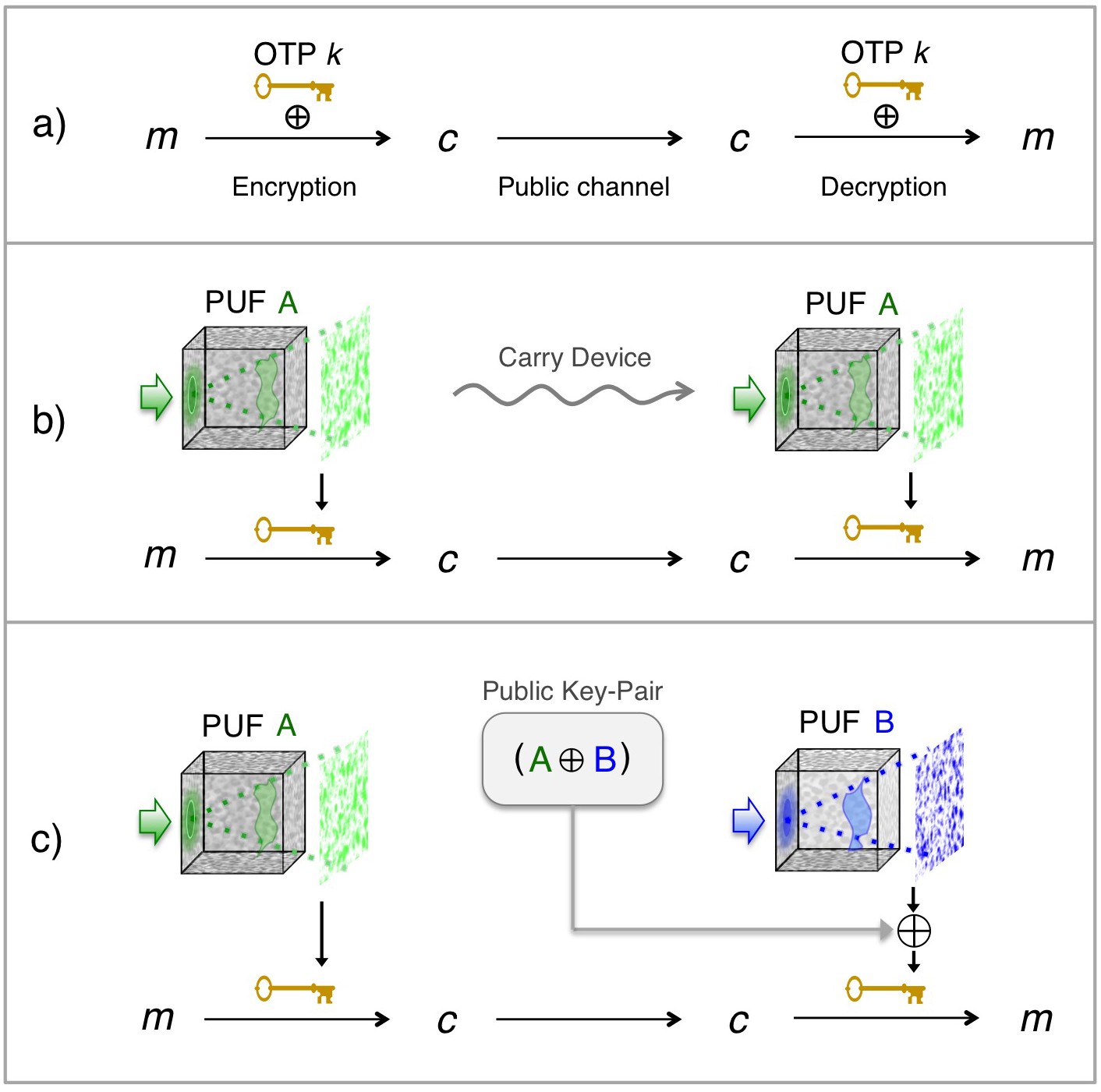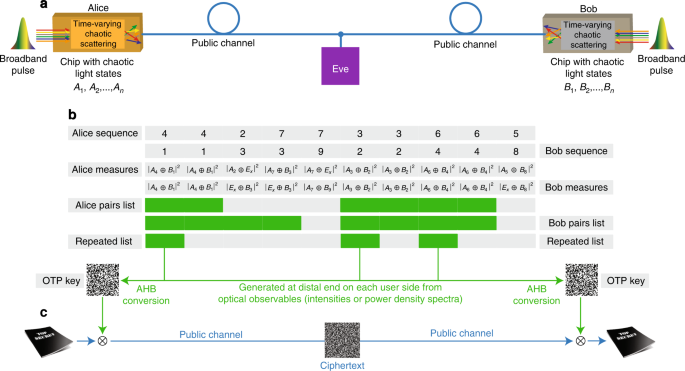
Perfect secrecy cryptography via mixing of chaotic waves in irreversible time-varying silicon chips | Nature Communications
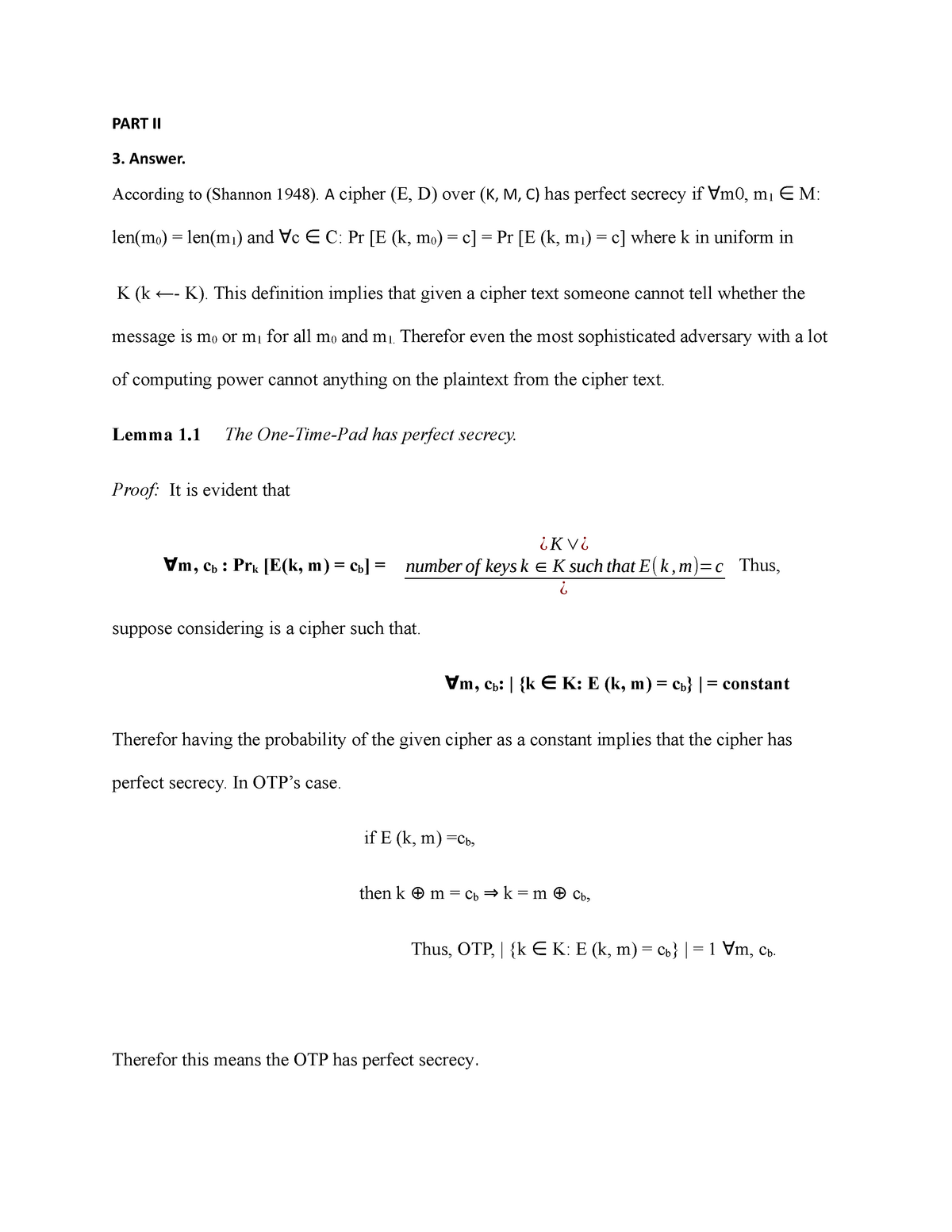
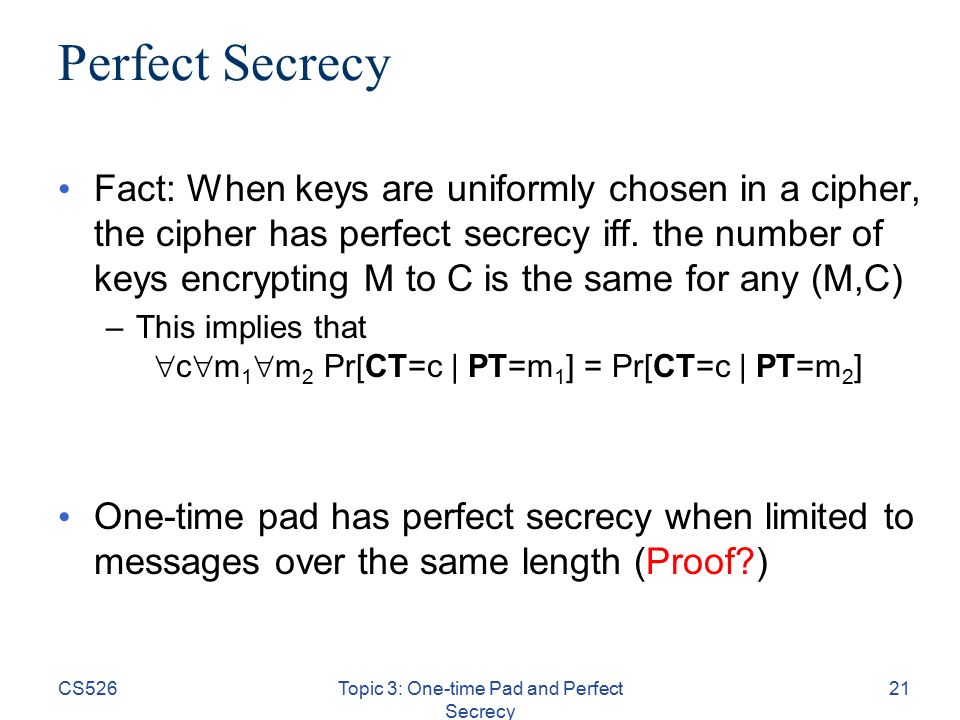
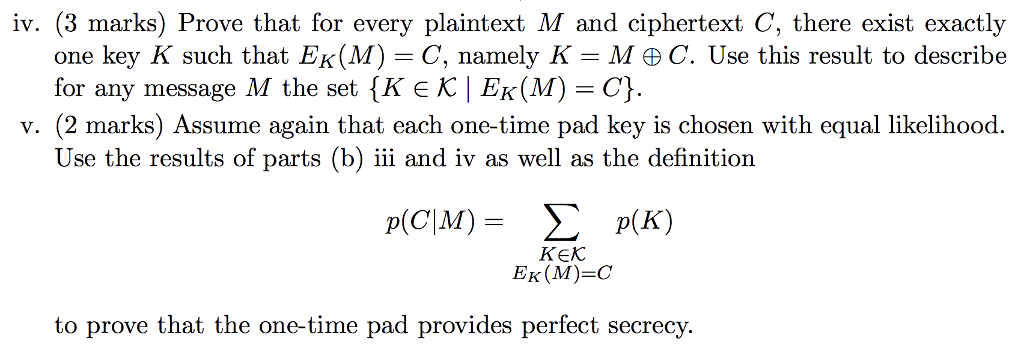
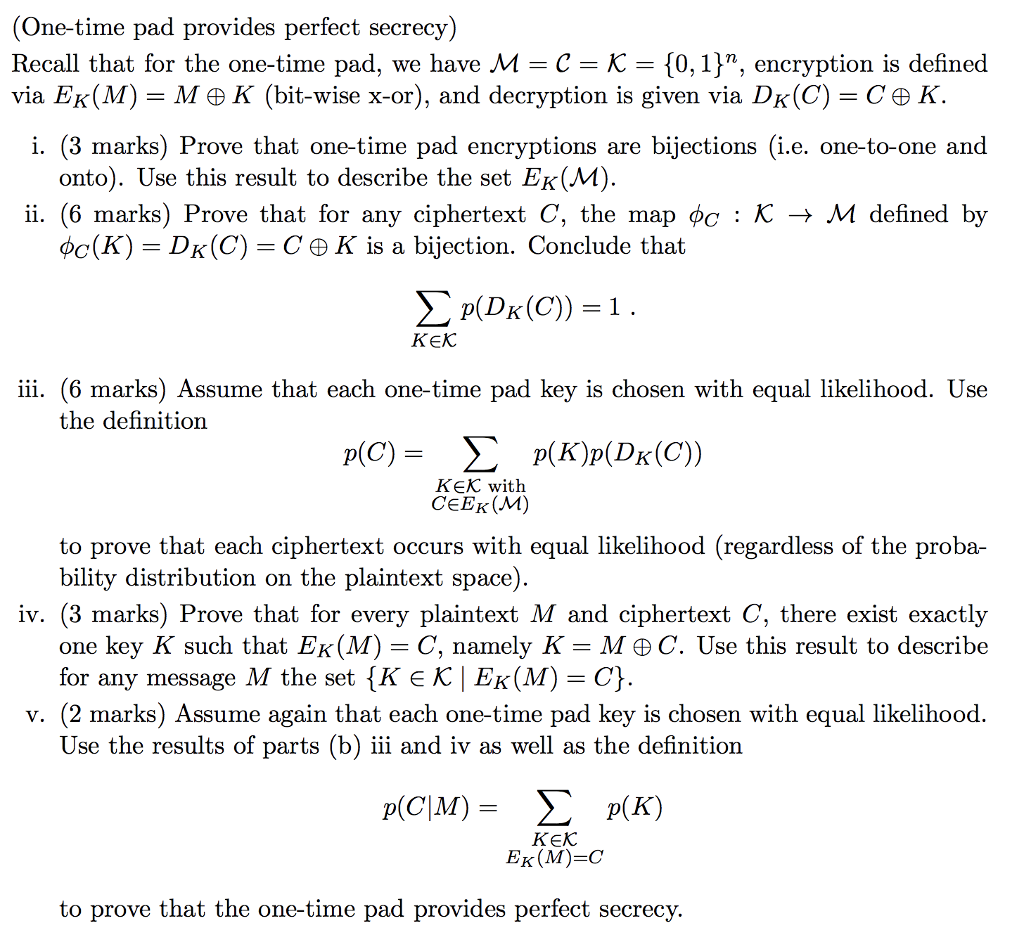
PART II - good - PART II 3. Answer. According to (Shannon 1948). A cipher (E, D) over (K, M, C) has - Studocu
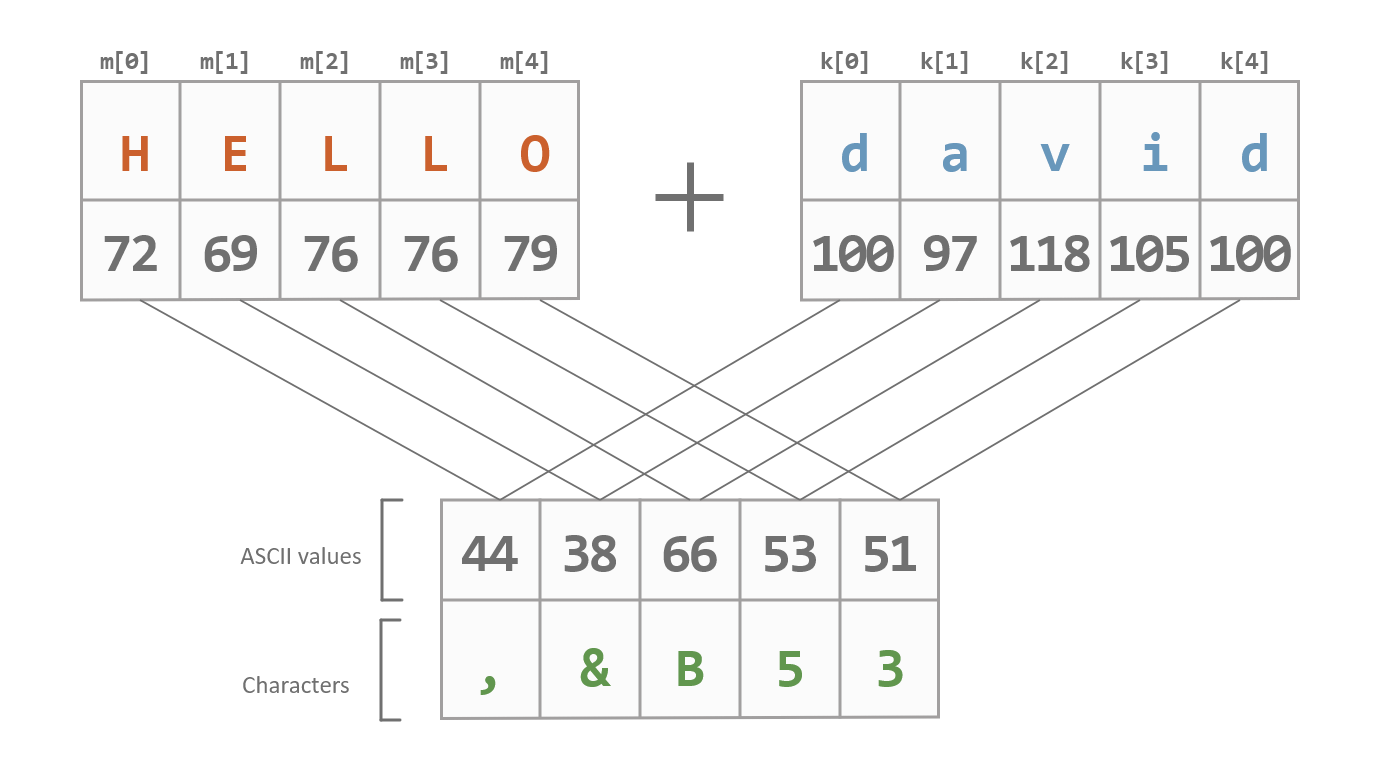
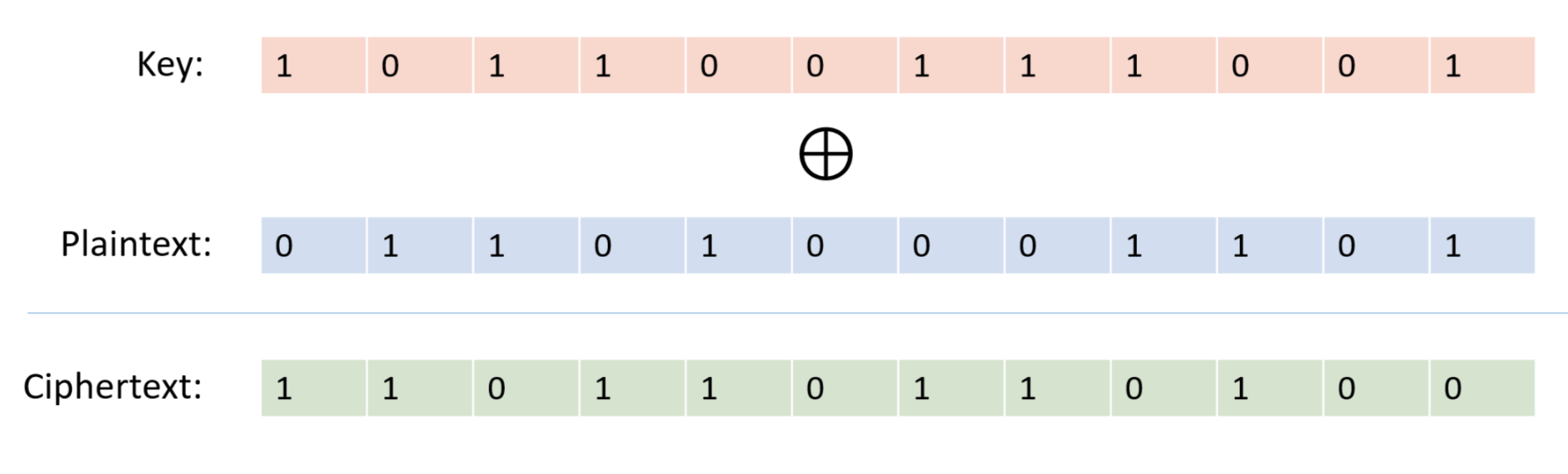
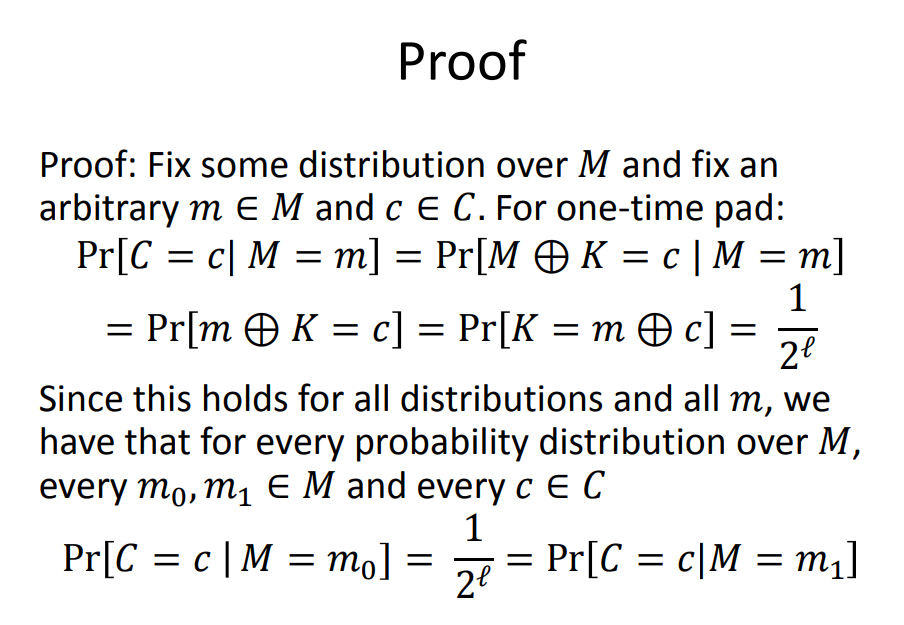
One Time Pad. This week, we will look at the one time… | by Oxbridge Inspire | Oxbridge Inspire | Medium

cryptanalysis - What are some real-world examples where one-time-pad encryption is used or can be used? - Cryptography Stack Exchange